Forging a Secure Tomorrow: Duke Energy’s Path to a More Resilient Future
An Interview with Mark Aysta, Duke Energy’s Managing Director of Enterprise Security
There’s a great quote by Confucius that says: “Our greatest glory is not in never falling, but in rising every time we fall.” And it’s truly applicable for security professionals because no matter how much one plans, strategizes and fully commits to preventing an incident, along comes something that challenges those efforts in ways that can help an organization grow, evolve and achieve an even better security posture.
On Dec. 3, 2022, Duke Energy experienced a “something” in the form of an unprecedented and sophisticated attack on a low-level substation that knocked out power to more than 40,000 residents in Moore County, North Carolina. Remarkably, Duke Energy had the power back on to all residents only a few days after the attack, a testament to the resiliency plans and talented teams it already had in place prior to the attack.
However, this event sent ripples throughout the industry that eventually made their way to Capitol Hill. We saw lawmakers on television publicly expressing concerns about what can be done to better strengthen utility security. This sort of pressure could have created enough internal and external strife and turmoil to derail a utility’s security efforts moving forward. But rather than let that pressure impact it, Duke Energy chose to rise to the challenge. They looked inward and further empowered its entire organization to adapt and evolve its security efforts so that it can better prevent and respond to threats and attacks.
Recently, I sat down with Mark Aysta, Duke Energy’s Managing Director of Enterprise Security, to talk about the company-wide effort to strengthen security through investment in new solutions, building stronger relationships with law enforcement, finding faster and stronger resiliency strategies and getting further left of boom through intelligence and data collection.
Curtis Marquardt, Jr:
Can you tell our readers a bit more about yourself and the security work you do with Duke Energy?
Mark Aysta:
I was born and raised in northern Minnesota, not far from the Canadian border. My family owned a milk business, and from the age of six until I was 18, I worked on milk trucks. It was hard work, and I realized it was not something I wanted to do for the rest of my life. So, I went to college and became a police officer. Then I earned my master’s degree and entered the FBI, where I worked as a special agent for more than 21 years. I retired from the FBI in December of 2018, and then had the opportunity to work at Duke Energy.
In my role at Duke Energy, I lead the corporate security team and am responsible for a variety of traditional corporate security functions like the administration and operation of the physical access control systems; video surveillance and management systems; 24/7 physical security operations center; uniformed security officers; executive protection; background investigations; security risk and compliance; digital forensics and incident response and data security.
In addition, I have oversight of some very unique areas to include the intelligence team, which seeks to identify and mitigate threats from external threat actors. I also manage our insider threat team, which endeavors to identify and mitigate risk from within the company. And, I have responsibility for the business continuity and emergency management programs that enable us to be resilient in the event of a crisis. We conduct yearly evaluations on those plans to ensure they are updated and then test them during drills and exercises.
Curtis Marquardt, Jr:
You mentioned your experience in law enforcement and a long tenure with the FBI. How has that career experience shaped your perspective as a security professional at Duke Energy?
Mark Aysta:
That’s a great question, and I can say that my perspective—as well as my strategy—was shaped because of the attacks on September 11, 2001. Prior to those events, I was a young FBI agent working bank robberies, kidnapping and violent crime—and there is no organization in the world better than the FBI at that type of work. FBI Agents are extremely skilled at gathering evidence, building cases and prosecuting the subjects who break the law. That was a great model for the first hundred years of the FBI. But with the September 11th attacks, that model did nothing to stop the murder of 3,000 of our citizens and things had to change. Various agencies within the intelligence community had separate pieces of intelligence about the attack, yet they failed to connect the dots and stop it.
That resulted in a monumental shift in thinking for the FBI and the intelligence community. The FBI’s primary mission became prevention of terrorist attacks, with the investigation and prosecution of the threat actors secondary. During my tenure there, I saw the entire FBI shift and retool substantially to achieve this goal of stopping attacks. That experience shaped my strategy when I came into Duke Energy. Our goal is to identify threat actors; identify their tactics, techniques, and procedures; access the level of maturity and timeline; and then stop that attack before it happens. Additionally, and in parallel with those efforts, we also work to maintain a robust strategy of resiliency that allows us to recover more quickly if we are attacked.
Curtis Marquardt, Jr:
We got to see that resilience strategy work exceptionally well with the December 2022 attacks on the Moore County substations. Duke Energy had power back up and running in a remarkably short period of time. Now, I know the attack is still being actively investigated, and I know there are specifics that can’t be discussed. But I do want to ask—from a high-level security perspective—how has Duke Energy adapted in ways that have further empowered the organization’s security moving forward.
Mark Aysta:
December 3rd was a significant event for our company. For the first time ever, a man-made incident caused 45,000 customers to lose electric service and it was an all-company effort for us to restore power for our customers. After witnessing the incredible work done by our teammates to restore service so quickly, I am very proud to work for Duke Energy.
Since that event, we have formed a team of not only security and transmission teammates but also communications, legal, generation and more. The focus of that team became the development of a new strategy to protect our assets and ensure the continuity of operations. Prior to the Moore County attack, Duke Energy—like every other utility in the country— focused on security controls built around protecting the bulk electric system. Any security controls like locks and fences at lower tiered sites were designed to keep the public out and away from the risk of injury by the equipment. But the Moore County attackers went after a low-criticality transmission substation. The tiering level of an asset didn’t matter to our customers in Moore County. All they knew was that the power was out.
So, the company did a comprehensive review of every asset we maintain. We had in place a criticality tiering system and we expanded on that system to include not only bulk electric system assets but also radial-fed assets and enhanced protection plans.
With this new strategy, we put an equal emphasis on resiliency. We enhanced emergency action plans for every asset, so if it is damaged by weather, an animal or a human, we know exactly what it will take to get that substation back in operation. Although it sounds easy, it was a significant effort given the size of our seven-state footprint and the thousands of assets that we operate.
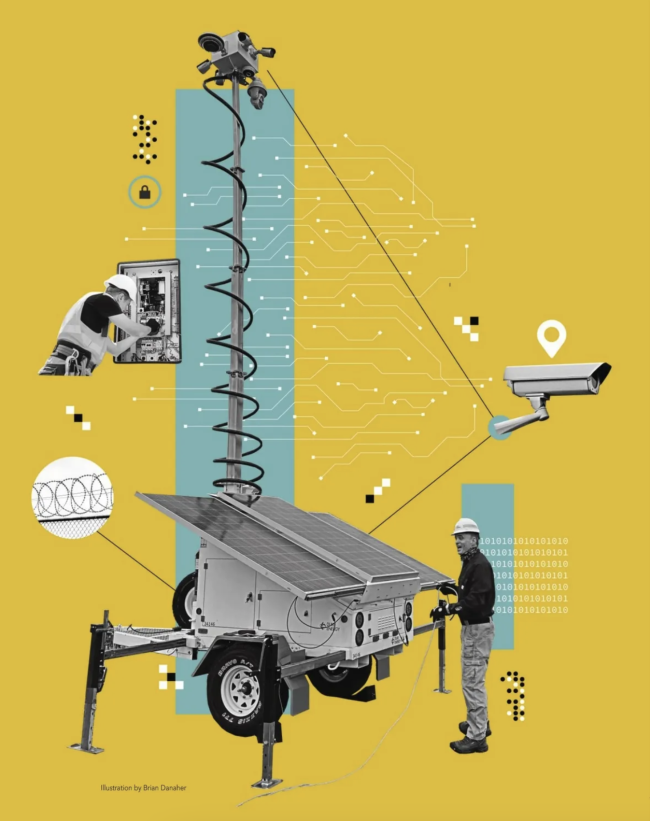
I’m not going to discuss the specific security upgrades we made, other than to say we have made a significant financial investment in upgrading our security controls. We are leveraging technology in new and exciting ways that utilize the philosophy of defense in depth.
In addition to the security and resiliency upgrades, we have put significant work and effort into the training with law enforcement partners. When I worked in law enforcement, I had no idea how the grid operated. So I knew we had to go out and provide that information.
So, we started a campaign to educate law enforcement officers about how the grid operates and the importance and vulnerabilities of our assets. We’re educating them on what suspicious activity looks like and how to respond to it. The training resonates with our law enforcement partners because they understand the criticality of our operations and the consequences that outages have on public safety.
Post 9/11, every state has a fusion center whose mission is to be the central point of collection, analysis and dissemination of threat information. By developing strong relationships with these fusion centers, we are helping them achieve greater visibility into the threats and suspicious activity we are seeing. I’ve got teammates across our seven-state footprint who have been certified as private-sector field liaison officers at the fusion centers, allowing for a seamless exchange of threat information.
Curtis Marquardt, Jr:
Let’s shift gears and talk more about security as it relates to threats from abroad. Headlines of late are all about physical and cyber efforts by adversary nation-states to infiltrate utilities in the U.S. What are your thoughts on these sorts of threats, and what is the best path forward?
Mark Aysta:
Whether it’s international or domestic, we’re going to treat threats the same way. We are going to understand what the threats are. We’re going to understand what the tactics, techniques and motivations of the threat actors are. We’re going to understand the maturity level of their operations, and then we’re going to mitigate accordingly, regardless of the origination of the threat.
With any successful attack, there’s going to be pre-operational activity that occurs. A threat actor intent on damaging our assets is not going to attack the first time they are there. They will spend time on scene surveying the layout, determining routes of ingress and egress, assessing the tools or weapons they will need, identifying the security controls in place, and making an assessment on the efficacy of attacking that site. By understanding what our critical assets are and deploying security controls that alert us when there’s anomalous activity, we can surge resources to the area during that pre-operational phase and stop an attack before it occurs. Again, the origination of the threat actors at this point are irrelevant.
Curtis Marquardt, Jr:
You mentioned earlier that Duke has invested in new technology in several areas. As these technologies continue to advance at a rapid pace, how do you keep your finger on the pulse of those changes? And how do you prepare for and adjust to them?
Mark Aysta:
This is part of understanding not only what the threats are but also what you’re mitigating. It’s about really staying abreast of the technology. Everybody’s got the next greatest thing and the “one tool” to protect you. But there is not one magic technology. We must use multiple layers of overlapping security controls. We need to understand what technology exists and how it would work in the environment. Then you pilot the equipment to determine how well it works before committing to it. You must remain brand agnostic and avoid getting married to a single technology.
Curtis Marquardt, Jr:
What do you view as the most challenging part of physical security at a utility?
Mark Aysta:
There are a lot of challenges, and I don’t think there is any “one thing” answer here. At Duke Energy, over the next 10 years, we plan to spend $70 billion on modernizing and securing the grid. We are seeing tremendous growth on our journey toward cleaner energy and are building renewable assets at a rapid pace.
What I see as a challenge is how to protect renewable generation like battery storage, solar and offshore wind. How do we strike that right level of spend versus what do we need to protect? We must view it through the lens of criticality and resiliency all while being conscious of the cost and impact to our rate payers.
Curtis Marquardt, Jr:
Every chef has his or her special ingredient that elevates the dish they’re creating. What’s the special ingredient that Duke Energy has that elevates its security posture to the next level?
Mark Aysta:
The secret recipe is and always will be the people. Our security team has a mission statement which is “to protect our people, our assets and our ability to power our communities.” As we move forward, our vision is to be an intelligence-driven organization that strives to identify and mitigate attacks before they occur. No organization could accomplish this vision if its people have not bought into it.
So, my challenge as a leader is to inspire teammates to embrace the mission, be creative, thoughtful and not fall back on doing things the way we always have. As the threat landscape changes, so do we. We need to look at new ways to protect, prevent and to become more resilient.
My greatest success in my five years with Duke Energy is that my team has embraced the vision. Now that they have internalized it, they are executing on it. They are being thoughtful and creative in solving problems in ways I could have never imagined—and it’s special to be a part of that effort.
Curtis Marquardt, Jr:
Thank you for your time today. To wrap this up, I want to ask you some questions I like to ask at the end of every interview: If you were to look into your security-specific crystal ball, what do you see coming five years from now? How about 10 years from now? What new challenges will be emerging, and what new solutions will come into play?
Mark Aysta:
Thank you for taking time to chat. To answer your questions, we know “AI” is the buzzword right now. And we need to know and understand how it can be used against us, but also how we can use it to enable safe, reliable and secure operations. As an example, we have deployed our first AI project to reduce the routine tasks in our Security Operations Center, freeing up our operators to focus on true security events. We can use AI to provide higher fidelity alarms so we don’t get lost in the noise of nuisance alarms. And we can use AI to conduct health checks on our equipment so that we have confidence that it is working and we can rapidly repair it when its broken. We must embrace technology advancements, but do so with a thoughtful, measured approach that includes governance.
In 10 years I suspect things will look entirely different in the physical security world. We will still have locks, cameras, fences, and security guards. But the technology we use—and how we use it—will be very different. My hope is that our entire sector will embrace the philosophy of being proactive and strive to stop the attack before it happens while fully embracing resiliency and rapid recovery when we can’t. Our customers and communities are counting on us.